The virtual data room has long been trusted by companies around the world and has shown that it can keep confidential company data intact during M&A transactions and any other financial transactions. For this purpose, VDRs use different protection methods and additional security measures, among which there is watermark protection. This protects your document from data leaks as well as from tampering and unauthorized access.
Watermarks in VDRs – why are they useful?
Today, watermarks are widely used in various fields, they denote an unauthentic bill as well as protect confidential documents from leakage inside the virtual data room. They form a small mark in the form of the name of the user who uploaded the document to the space along with the date and time of the upload. This marking is invisible, but thanks to it users will be able to track their documents even outside the company.
VDR providers offer different online dataroom watermarks, among them dynamic ones, some offer to customize and create the watermark, some offer watermarks in the form of a company logo to clearly indicate the rights on a document (e.g. a project). This feature is a great addition to protection during due diligence, mergers and acquisitions, fundraising, and other financial transactions.
Other VDR security features
Other ways to protect sensitive data rooms include the following features:
- Self-destructing documents-you can control access to documents in real-time and revoke access to them at any time
- 256-bit encryption – This method of encryption meets the highest modern security standards – any data that enters your data room is securely encrypted and protected from data leakage
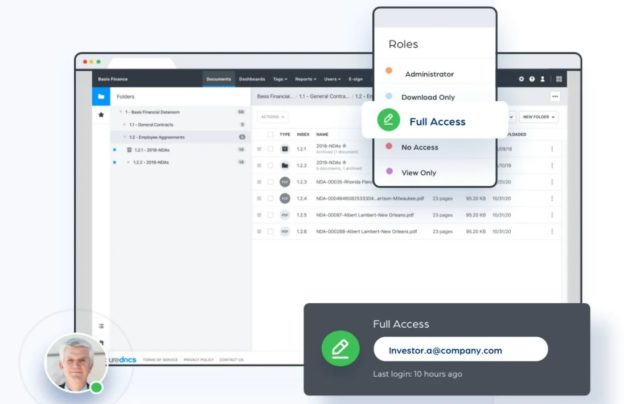
- Access restrictions for documents – the administrator himself can select which functions and permissions he may assign to a document, and who may see this document. You also select the levels of data protection. You can prohibit copying, printing, editing, forwarding, or downloading the document. Permissions can be set on the basis of roles or manually
- Data backup – Constant backups are a very useful feature that serves you as a backup plan. You do not have to worry about the integrity of your data even if it has been damaged, because you can easily restore it
- Automatic virus scanning – VDR’s built-in anti-virus checks any file you want to add to the space before it’s downloaded
- Open encryption/on-save – The first encryption method means that documents are automatically encrypted while they are running. This is how VDR vendors try to secure your data from unauthorized viewing. And when you save, encryption protects the data that is inside your storage, i.e., security at rest
- Access from mobile devices – an authorized user can access the data room and its information anywhere and from any device, but the data is still secure
- Multistep verification -If you want to access the program from a device that was not previously used for this purpose, be prepared for multi-step verification which makes sure that you are not an intruder
- Complex Logon is an additional layer of protection that focuses on logging in. It protects your password, so when logging in you will have to enter a one-time code to be sent to your cell phone in addition to your username and password